A PoC project to help identifying networks leaking ephemeral ports.
According to this article, the following files
/proc/net/tcp
/proc/net/tcp6
/proc/net/udp
/proc/net/udp6
provide (aka netstat) details about TCP/UDP connections currently open under Android OS. Process or app uid is also revealed in those files.
Using simple code like this, it is possible to find the actual package name of the app that created the connection.
Some of the networks, notoriously WIFI ones, preserve ephemeral port number of the TCP/UDP packets leaving the system. Using this project, it is possible to detect if the network, your device is currently connected to, leaks this information.
This is a screenshot of the Android app in action. Building it requires Android Studio.
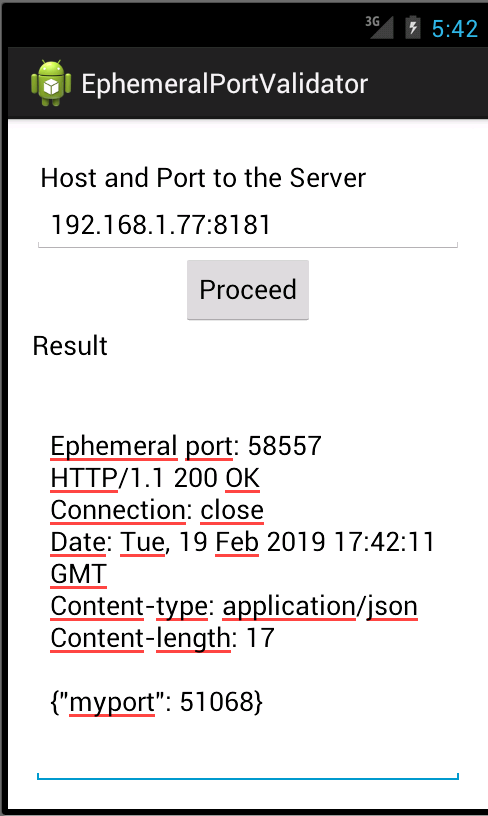
If myport (as reported by the remote server) and Ephemeral port values are the same, then the network leaks ephemeral port details.
simple-webserver folder contains the code for the server side. It's a small Java console application, based on some of the old Sun undocumented features coming with the JDK. Very handly whenever I need to sketch a quick web server behaviour.