PacketSnitch is a Python tool for extracting payloads and rich metadata from network packet capture (.pcap) files. It generates testcases for fuzzing, protocol analysis, and research by saving raw packet data and detailed information about each packet, including protocol, entropy, geoip, banners, and more. The tool optionally performs active reconnaissance to enrich output with server banners, SSL certificate info, and web page titles.
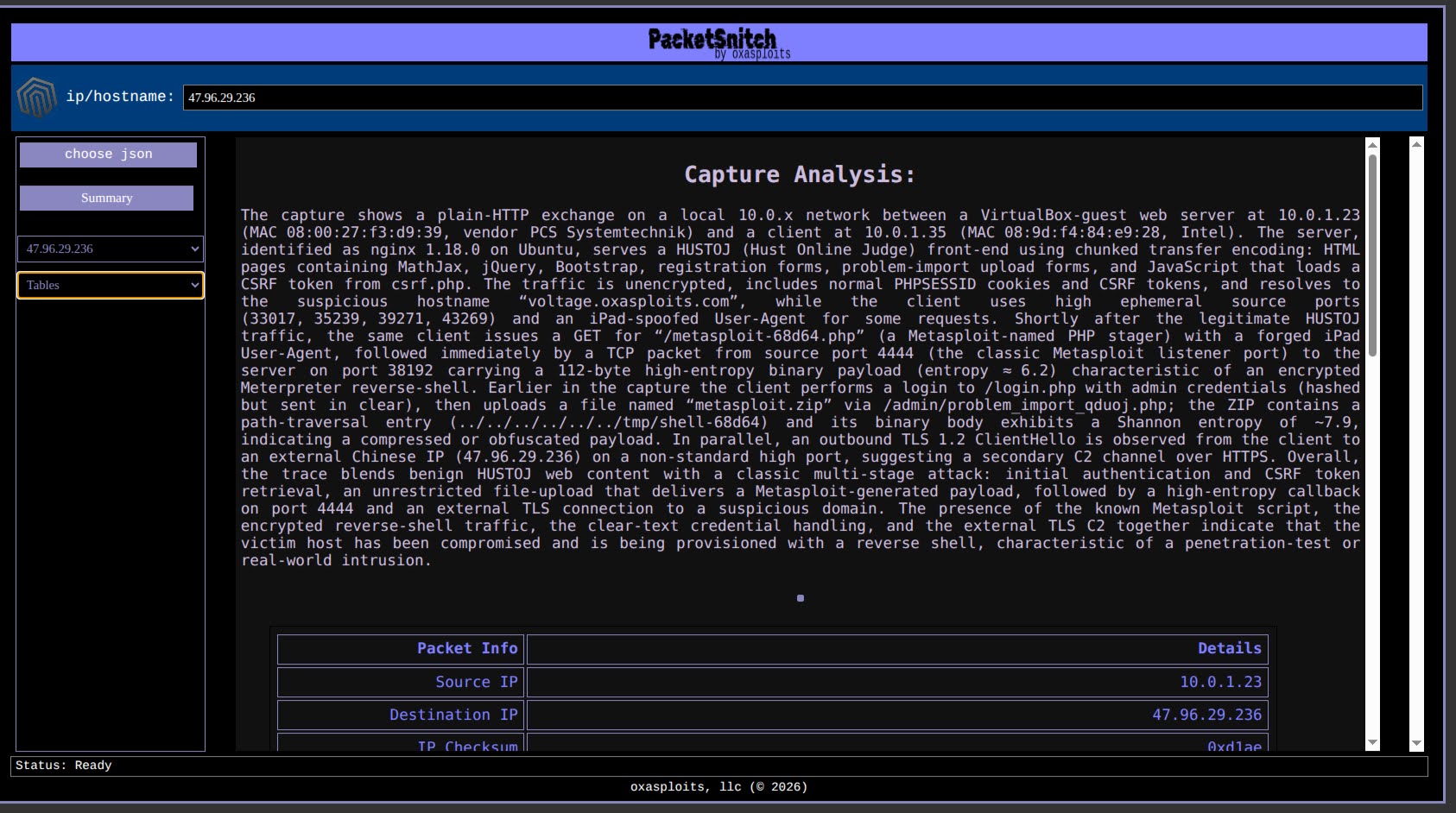
This is a screenshot of the frontend (while still in heavy alpha development).
- Extracts TCP payloads from
.pcapfiles and saves them as binary testcase files. - Generates JSON info files for each testcase, containing:
- Packet metadata (timestamps, MAC/IP addresses, ports, flags, checksums)
- MIME type and magic description
- Shannon entropy and character statistics
- GeoIP lookup for source/destination IPs
- Port descriptions (ICANN database)
- MAC vendor lookup
- Active recon: server banners, SSL certificate info, web page titles (optional)
- Consolidates all testcase info into
all_testcases_info.json. - Supports filtering by source/destination port.
- Handles compressed payloads (gzip/zlib).
- Verbose/debug output modes.
Commercial
Commercial
Marshall Whittaker
