Cybersecurity | Network Security | Cloud Security
Building hands-on labs in AWS, Cisco networking, and malware traffic analysis
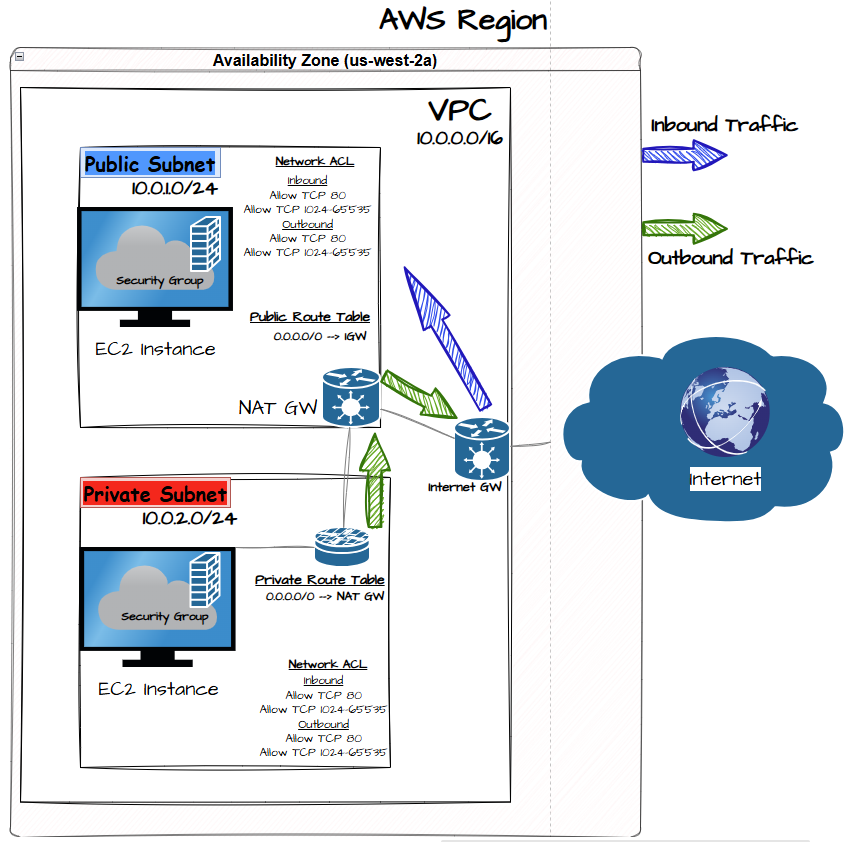
Designed and deployed a segmented AWS network architecture using a VPC, public and private subnets, NAT Gateway, Internet Gateway, route tables, and Network ACL security controls.
Technologies AWS VPC • EC2 • NAT Gateway • Internet Gateway • Route Tables • Network ACLs
🔗 Project Repository
https://github.com/mrtnzjhonatan/aws-vpc-secure-infrastructure
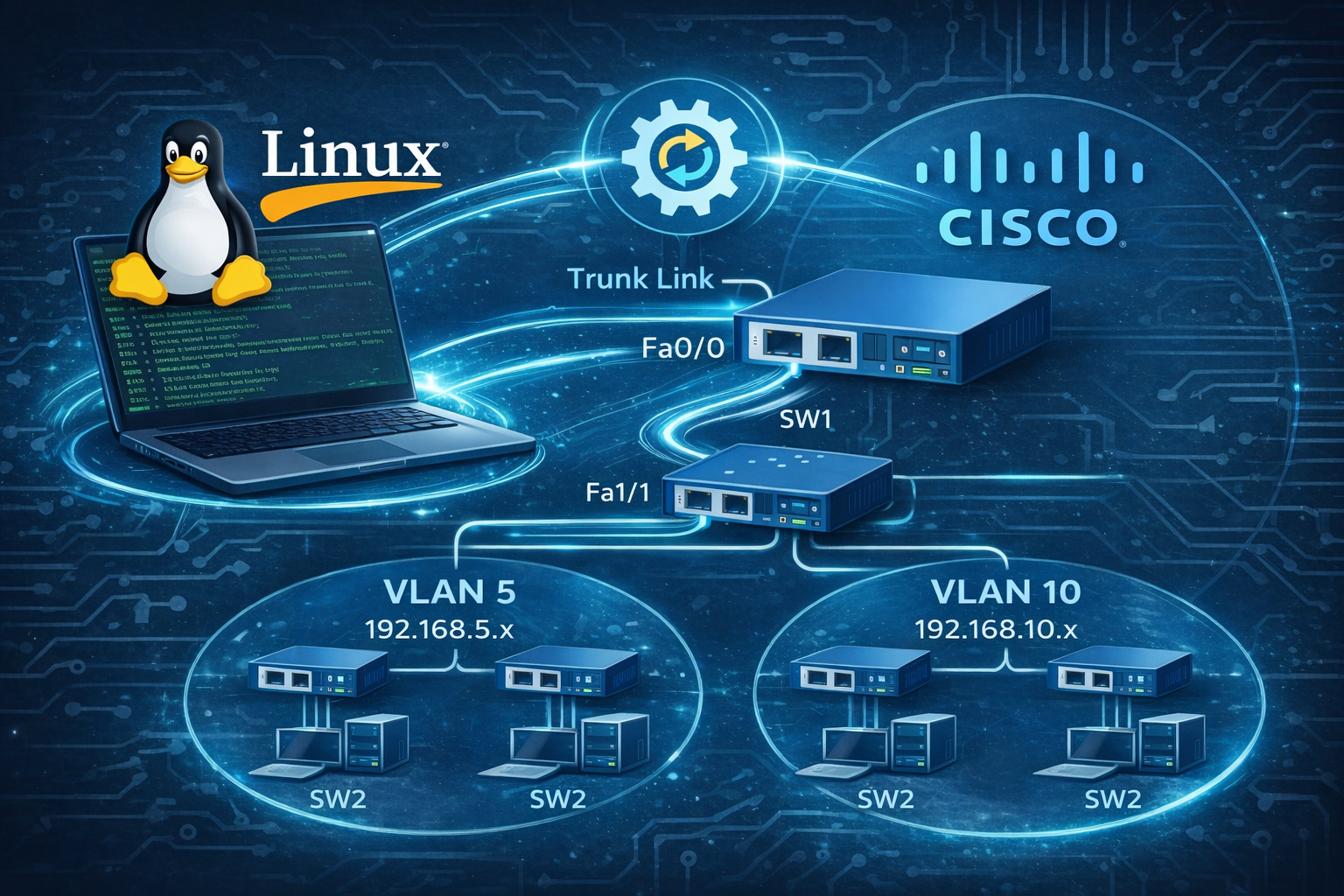
Designed and implemented a Router-on-a-Stick network topology to enable inter-VLAN communication between segmented networks.
This lab demonstrates how Cisco networking can be practiced using Linux-based tools such as Dynamips, Dynagen, and VPCS without requiring physical hardware.
Key concepts demonstrated:
- VLAN segmentation
- Inter-VLAN routing
- 802.1Q trunk configuration
- Router subinterfaces
- Layer 2 and Layer 3 connectivity troubleshooting
- Cisco router and switch configuration in a Linux environment
🔗 Project Repository
https://github.com/mrtnzjhonatan/Router-on-a-Stick-VLAN-Network
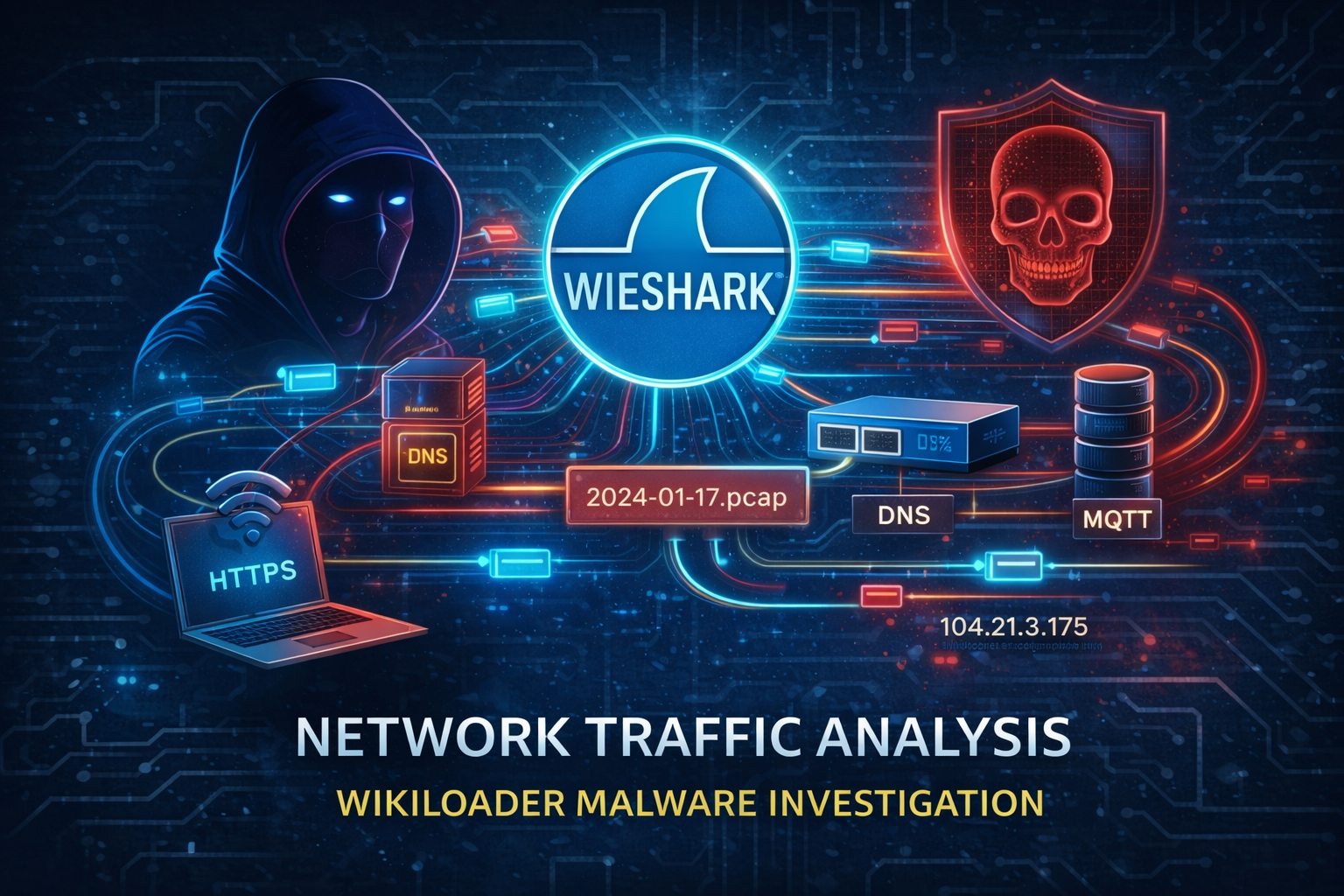
Performed network traffic analysis on a compromised host using Wireshark to identify suspicious communications and potential Indicators of Compromise (IoCs).
The investigation focused on analyzing encrypted HTTPS traffic, inspecting TLS handshake metadata, reviewing DNS query behavior, and identifying command-and-control communication over the MQTT protocol.
Key findings included suspicious traffic associated with the Wikiloader malware family, including connections to potentially malicious domains and repeated DNS queries indicating persistent external communication.
Skills Demonstrated
- Network Traffic Analysis
- Wireshark Packet Inspection
- Threat Hunting
- DNS and TLS Analysis
- Identifying Indicators of Compromise (IoCs)
🔗 Project Repository
https://github.com/mrtnzjhonatan/network-traffic-analysis
🛡️ Cybersecurity Professional with hands-on experience in offensive and defensive security techniques. Ranked in the Top 1% on TryHackMe with over 215+ rooms completed and 29+ badges earned. I specialize in:
- 🔍 Threat Detection & Blue Teaming
- 🧠 Vulnerability Assessment & Exploitation
- 🐧 Linux Privilege Escalation
- 🛠️ Network & Web Application Pentesting
- ✅ Jr Penetration Tester (30h 40m, Completed June 2025): View Certificate
- ✅ Security Engineer: View Certificate
- ✅ Intro to Cyber Security: View Certificate
- ✅ Pre-Security: View Certificate
| Category | Tools / Skills |
|---|---|
| 🔐 Offensive Security | Nmap, Burp Suite, Metasploit, Hydra, SQLMap |
| 🛡️ Blue Teaming | Wireshark, OSQuery, Splunk, Sysmon, Yara |
| 📡 Networking | TCP/IP, DNS, Routing, VLANs |
| 💻 OS Knowledge | Linux (Debian, Ubuntu, Kali), Windows AD |
| ⚙️ Scripting | Bash, Python (basic automation), PowerShell |
🧩 View all rooms: TryHackMe Profile
🛠️ Cybersecurity Labs Repo
📝 Write-ups, tools, and hands-on walkthroughs from TryHackMe rooms
- 🧑💼 LinkedIn: Jhonatan Martinez
- 💻 GitHub: @mrtnzjhonatan
I am actively advancing my cybersecurity knowledge through Hack The Box Academy. Below is a list of completed modules and badges demonstrating hands-on skills in networking, Linux, enumeration, and exploitation.
- 🧠 Learning Process
- 🚀 Intro to Academy
- 🐧 Linux Fundamentals
- 🌐 Network Enumeration with Nmap
- 🛡️ Introduction to Networking
- 💣 Using the Metasploit Framework
- 🐍 Introduction to Python 3
- 🔧 Network Foundations
| Badge | Description |
|---|---|
| Badge | Solid Basis - Network Foundations |
| Badge | Binary Duo Explorer - two years of learning at HTB Academy |
| Badge | PThe eye that sees all - Network Enumeration with Nmap |
| Badge | Our favorite seabird - Linux Fundamentals |
| Badge | Everything is connected - Introduction to Networking |
| Badge | Snake Charmer - Introduction to Python 3 |