Advanced Asynchronous Web Fuzzer & Recon Engine
High-Speed • Intelligent • Stealth-Oriented
🇧🇩 Developed by BLACK ZERO
🛡️ Powered by BANGLADESH CYBER SQUAD
Site Hound is a modern, high-performance web fuzzing framework designed for deep reconnaissance and endpoint discovery.
Unlike traditional directory brute-force tools, Site Hound integrates:
- adaptive concurrency
- intelligent filtering
- header spoofing
- recursive discovery
- response analysis
to produce accurate, low-noise results at high speed.
- Built on
asyncio+aiohttp - Handles thousands of requests efficiently
- Non-blocking architecture for maximum throughput
- Automatic deduplication
- Comment & noise removal
- Bad character filtering
- Smart sorting and normalization
- Context-aware extension combination
- Prevents invalid payloads (
.env.php,.bak.bak) - Supports deep path fuzzing
- Content length comparison
- Hash fingerprinting (MD5)
- Word & line analysis
- Detects servers returning constant responses
- Prevents false positives
- Filter by status code, size, words, lines
- Match specific patterns
-
Dynamically adjusts request speed
-
Detects:
- rate limiting (429)
- server errors (5xx)
- latency spikes
-
Auto reduces or increases concurrency
- Requests-per-second control
- Prevents detection & blocking
- Automatic retry on failure
- Smart delay handling
-
Generates realistic headers:
X-Forwarded-ForX-Real-IPVia
-
Mimics proxy chains
-
Random IP rotation
-
Built-in real browser UAs
-
Custom UA support:
- file
- JSON
- manual
- Auto directory discovery
- Controlled recursion depth
- Deep fuzzing with path explosion
- Built-in crawler support
- Colored logs
- Real-time status updates
- Structured output display
- JSON → structured data
- CSV → analysis ready
- TXT → raw output
pkg update && pkg upgrade -y
pkg install git python -y
git clone https://github.com/TEAMBCS/Site-HOUND.git
cd Site-HOUND
chmod +x *
pip install -r site-hound.txt
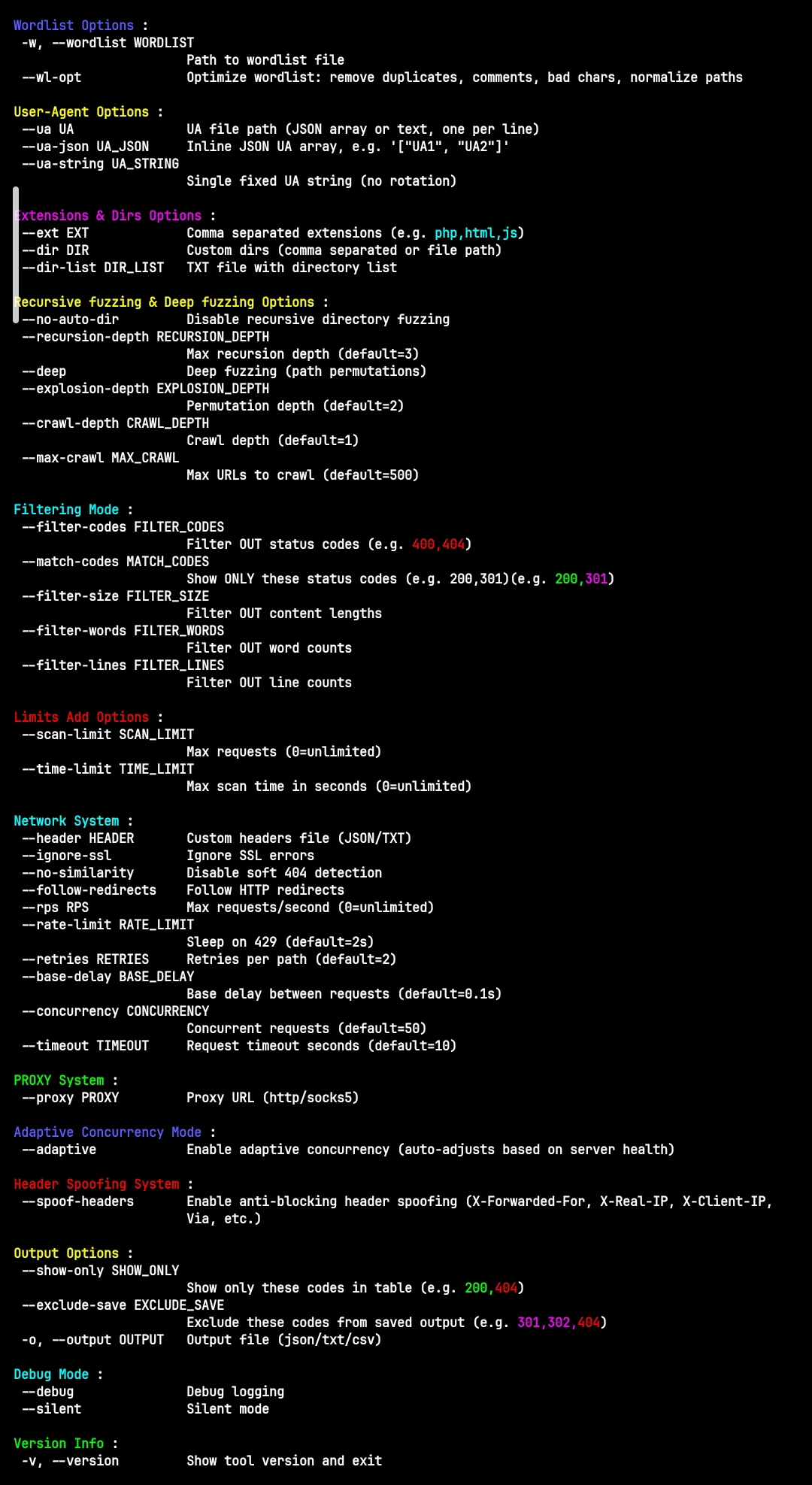
python3 site-hound.py -hpython3 site-hound.py -u https://target.compython3 fuzz7.py \
-u https://target.com \
-w wordlist.txt \
--ext php,html,json \
--concurrency 80 \
--adaptive \
--spoof-headers \
--recursion-depth 3 \
--rate-limit 15 \
--timeout 10| Argument | Description |
|---|---|
-u, --url |
Target URL |
-w, --wordlist |
Wordlist file |
--ext |
File extensions |
--concurrency |
Number of async workers |
--adaptive |
Enable adaptive concurrency |
--rate-limit |
Requests per second |
--timeout |
Request timeout |
--retries |
Retry count |
--proxy |
Proxy support |
--header |
Custom headers file |
--spoof-headers |
Enable header spoofing |
--ua |
User-Agent file |
--ua-json |
User-Agent JSON |
--recursion-depth |
Directory recursion depth |
--deep |
Enable deep fuzzing |
--crawl-depth |
Crawl depth |
--filter-codes |
Filter status codes |
--match-codes |
Match only specific codes |
Target Input
↓
Preflight Check
↓
Soft-404 Baseline
↓
Wildcard Detection
↓
Wordlist Optimization
↓
Async Fuzzing Engine
↓
Adaptive Concurrency Control
↓
Filtering & Validation
↓
Result Storage
- Admin panel discovery
- Hidden endpoint detection
- API enumeration
- Backup file detection
- Misconfiguration discovery
This tool is intended strictly for authorized security testing.
You must have:
- explicit permission
- legal authorization
The developer assumes no liability for misuse.
- 🔗 Dev: BLACK ZERO
- 🛡️ Team: BANGLADESH CYBER SQUAD
Contributions are welcome.
- Fork the repo
- Create a branch
- Submit a pull request
If you find this project useful:
- ⭐ Star the repository
- 🔁 Share with others
- 💡 Suggest improvements
Precision over noise Speed with control Stealth by design